Product Catalog
Our Digital Store
Explore our curated collection of professional tools, digital assets, and high-fidelity technical resources.
Latest Arrivals
Featured Catalog Items
E-book
Digital E-Books
Browse our collection of specialized technical books.
$49.99
View Services →
Software
Software Licenses
Genuine licenses for professional tools.
$199.99
View Services →
Design
Digital Design
High-end UI/UX and branding for digital products.
$1,499.99
View Services →
Video
Video Production
Professional cinematic production and post-processing.
$4,999.99
View Services →
IPTV
IPTV Streaming
Premium streaming subscriptions with international protocol access.
$29.99
View Services →Resource Library
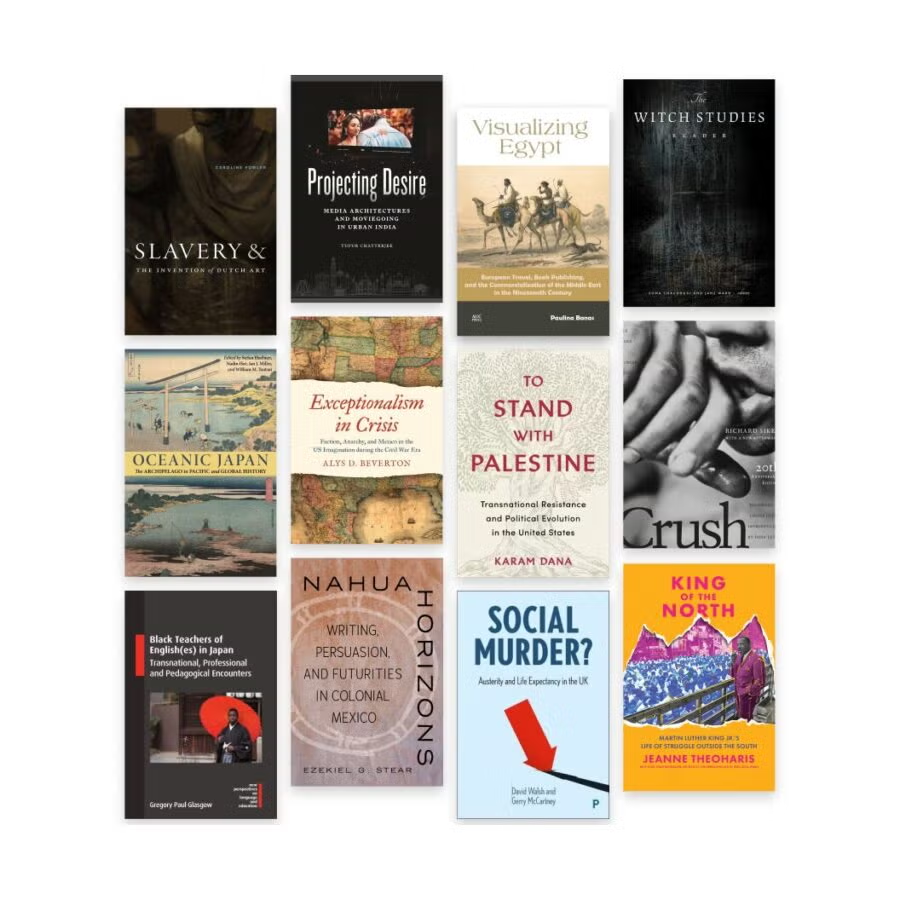
Featured E-books
Syncing library data...
Global Delivery
Instant digital dispatch for all assets.
24/7 Support
Our team is always available to assist.
Secure Licensing
All products are verified and authentic.